yum upgrades for production use, this is the repository for you.
Active subscription is required.
📅 Updated: November 14, 2020 (Originally published: September 4, 2018)
The best protective measures you can take for your Magento site’s administration area are:
- Allowing access to the admin area for specific IP addresses only
- Renaming admin area
However, what can you do to protect Magento if you simply don’t want to use IP whitelisting and instead want to keep your Magento admin area accessible from any IP address? Or how can you further improve security, provided there’s always a possibility that one of your trusted (employee’s) IP addresses is compromised?
Meet Fail2ban
Fail2ban can help you ban intruders early. It is great in its flexible approach of monitoring log files for failed login attempts and banning respective IP addresses.
Even if you’re using IP whitelisting for access to the Magento area, you can still complement it with Fail2ban. This covers a case where an employee’s computer system was hacked, or malicious users have otherwise gained access to trusted IP addresses.
There are some resources online (like this article) which aim to provide configuration tips for Fail2ban + Magento. But what is the proper way?
The mentioned reference article fails to deliver proper banning in a few ways, mainly because:
- It uses “soft bad behavior”, which is simply checking for X number of attempts to log in. There is no distinguishing between successful and failed login attempts
- Scanning potentially large
access.logwill result in performance penalty incurred
Instead, we need to:
- Log failed login attempts in a distinguishable manner
- Configure Fail2ban to scan the log file for failed login attempts and ban those IP addresses
Let’s review the best practices approach towards protecting the Magento admin area with Fail2ban. There are two main components as we mentioned earlier.
1. Log failed admin attempts
One plugin that works for the purpose of logging failed admin attempts is Alarmbell Extension for Magento.
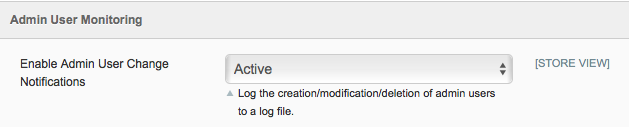
Simply install it and configure to write failed login attempts to the log file:
Now anytime a failed login occurs, we get a log entry to var/log/system.log in a form of:
2018-09-04T08:35:38+00:00 DEBUG (7): ALARMBELL (1.2.3.4): Failed admin user login for ‘admin’
2. Fail2ban jail and filter
All we need to do further is have Fail2ban scan the log file and search for those failed login entries. Fail2ban builds on the jail approach. A jail is a set of log files and respective search patterns for failed access. Typically, a search filter and jail go into separate files.
Let’s create our magento jail first:
/etc/fail2ban/jail.d/magento.conf
[magento]
enabled = true
port = http,https
filter = magento
logpath = /path/to/var/log/system.log
bantime = 7200
maxretry = 5
findtime = 600
We tell Fail2ban to search for failed login attempts in our Magento system.log file. 5 failed attempts within 10 minutes (600 seconds) will result in the ban of IP for 2 hours.
Obviously, you need to adjust the logpath with the actual filename of your Magento system.log.
Next, we should create the Fail2ban filter file that will hold regex of a failed login attempt:
/etc/fail2ban/filter.d/magento.conf
[Definition]
# 2018-09-04T08:35:38+00:00 DEBUG (7): ALARMBELL (1.2.3.4): Failed admin user login for 'Admin'
failregex = ^s+\w+ \(\d\): ALARMBELL \(<HOST>\): Failed admin user login
ignoreregex =
Note that in the servers supporting IPv6 connections, you’d really want to use Fail2ban > 0.10. That is the current stable version which does support IPv6. While the EPEL repository for CentOS 7 has only got releases from Fail2ban 0.9, we have got your covered, as our repository has a recent build of Fail2ban 0.10.

jonathonbook
Modified the regex slightly, this solution shut down non-stop brute-force attacks on an older 1.9 installation. Thank you, amazing how effective!