yum upgrades for production use, this is the repository for you.
Active subscription is required.
If you have a Magento 1.9.x shop running on CentOS/RHEL 7, visiting a specific page in the Magento administration area might upset you.
Navigate to System -> Configuration -> Sales -> Payment Methods and behold:
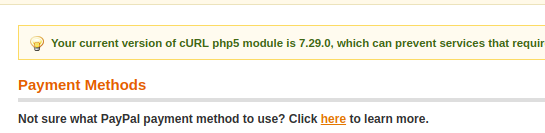
The complete message is:
Your current version of cURL php5 module is 7.29.0, which can prevent services that require TLS v1.2 from working correctly. It is recommended to update your cURL php5 module to version 7.34.0 or higher.
Do you really have to worry? Let’s dig in the details and find out for sure.
PayPal, TLS version and Magento
The story begins with PayPal not-so-new requirement to establish connections to its servers using TLS 1.2 protocol.
In regards to PayPal servers, your Magento server is a client. So the requirement, in a nutshell, is that Magento will talk TLS 1.2 to PayPal servers.
Magento runs with PHP engine, and PHP uses the libcurl library for most of the routines that involve making connections to external websites.
The TLS version is negotiated initially by the client (Magento) specifying the highest version that it supports among other parameters (cipher parameters, etc.).
The problem is that versions 1.1 and 1.2 of the TLS protocol were disabled by default in libcurl up to version 7.34.0. And thus Magento servers with the old library would fail to connect to PayPal servers. Or wouldn’t they? 🙂
libcurl and RedHat
RedHat tends to backport security fixes to its packages while preserving the functionality base (and thus the version numbers). This is good because your system is very stable and secure.
But this is bad, because it may be very confusing since a package may appear old by its version number, but actually have all the latest security fixes applied to it.
And this is exactly the case of confusion that happens with libcurl.
Even your libcurl package may be below 7.34.0, it may already include the fix to enable TLS 1.2 by default.
RedHat has applied the required change in this ERRATA (update). So you can conclude that any libcurl package starting from libcurl-7.29.0-25 onwards will work fine and allow your Magento to talk to PayPal servers using TLS 1.2 without any issue.
Magento check
The warning originates from app/code/core/Mage/Adminhtml/Block/Notification/Curl.php where it simply checks that the version of curl library used by your PHP is less than 7.34.0. Which is not the proper check as we know now. Perhaps, the better check would involve if (defined("CURL_SSLVERSION_TLSv1_2")).
Technically, the wording or the warning is not correct either because it really checking libcurl library version and not PHP curl module version. And php5 is mentioned even if you’re running your Magento 1.9 with PHP 7.2.
But what are the consequences of this simple buggy check and incorrect warning? People install newest libcurl en masse, all from third-party repositories. Which sure enough brings their system to risk and stability issues. Don’t do that too. We’re smart, eh?
The proper solution
- Simply run
yum clean allfollowed byyum update libcurlto install the latestlibcurl - Restart / reload PHP. E.g., for PHP-FPM:
systemctl restart php-fpm - Confirm that you can connect fine by placing a script in your site and running it
$ch = curl_init('https://tlstest.paypal.com');
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
$data = curl_exec($ch);
curl_close($ch);
echo $data;
The response should proudly say PayPal_Connection_OK.
Finally, now it’s OK to ignore the warning, even it’s there. Just close your eyes… _^_^_
Literature:
